Hexatech vpn wifi is it the secret weapon you need for secure browsing
Hexatech vpn wifi is it the secret weapon you need for secure browsing: Is It Your ultimate Tool for Online Privacy, Speed, and Safety?
Hexatech vpn wifi is it the secret weapon you need for secure browsing? Quick answer: yes, but with caveats. In this video-style guide, we break down how Hexatech VPN WiFi works, what it protects, who should use it, and how to optimize it for the best experience. Below you’ll find a practical, user-friendly breakdown, plus quick tips, data-backed insights, and real-world scenarios so you can decide if Hexatech VPN WiFi belongs in your digital toolbox. If you’re curious to explore a trusted option while you watch, check out our affiliate link for a trusted VPN provider—click here to learn more and possibly snag a deal: https://go.nordvpn.net/aff_c?offer_id=15&aff_id=132441
Hexatech vpn wifi is it the secret weapon you need for secure browsing? It’s a bold claim, but there’s real substance behind it. Here’s a quick guide to what we’ll cover:
- What Hexatech VPN WiFi is and how it works
- Core security features and encryption standards
- Performance considerations: speed, latency, and stability
- Privacy implications: logs, jurisdiction, and data protection
- Use cases: streaming, public Wi‑Fi, work-from-home, and travel
- Common myths vs. realities
- Setup, configuration, and best practices
- Comparisons with other VPNs
- Getting started: quick-start checklist
- Useful resources and further reading
Key facts at a glance
- Encryption: AES-256 or equivalent—standard for strong protection
- Protocols: OpenVPN, IKEv2, WireGuard depending on implementation
- Kill switch: yes/no depending on app version
- DNS leak protection: typically included
- Logging policy: varies by provider; check jurisdiction and policy
- Jurisdiction: where the company is registered affects data requests
- Price and trial options: often available; check current promos
- Compatibility: Windows, macOS, iOS, Android, and sometimes Linux or browser extensions
Useful URLs and Resources Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence Tor Project - www.torproject.org Electronic Frontier Foundation - www.eff.org VPN Pain Points - www.vpnmentor.com TechBenchmark Labs - www.techbench.org
What Hexatech VPN WiFi Actually Is
Hexatech VPN WiFi is a combination of a virtual private network service and a WiFi security layer designed to encrypt your internet traffic and obscure your device's IP address when you’re online, especially on shared networks. In practice, you’ll be routing your traffic through secure servers, which masks your location and activity from prying eyes—helpful on public networks like coffee shops or airports.
- How it works in simple terms: your data is wrapped in a protected tunnel from your device to the VPN server. Anyone intercepting traffic between you and that server should see only encrypted data, not your personal information.
- What it isn’t: a magic wand that solves every online privacy problem. No tool is 100% foolproof; the best approach combines VPN use with strong passwords, two‑factor authentication, up‑to‑date software, and good habit changes.
Core Security Features to Look For
When evaluating Hexatech VPN WiFi or any VPN, these features matter most:
- Encryption standards: AES-256 with an additional secure handshake
- Protocols: OpenVPN, WireGuard, and/or IKEv2 for speed and reliability
- Kill switch: ensures apps won’t leak data if the VPN drops
- DNS leak protection: prevents your real DNS from leaking
- Split tunneling: decide which apps use the VPN vs. direct connection
- Multi-hop double VPN: routes traffic through two servers for extra privacy
- Obfuscation: helps disguise VPN traffic in restricted networks
- No-logs policy: critical for privacy; check what is actually logged and for how long
- Jurisdiction: data retention laws affect privacy protections
Data and ranking
- A recent global VPN usage study shows that around 60% of respondents use a VPN primarily on public Wi‑Fi to prevent man‑in‑the‑middle attacks.
- Among top VPNs, users typically report improved security on public networks, with speed sometimes impacted depending on server load and protocol.
Public Wi‑Fi vs. Private Wi‑Fi: Why the VPN Matters
Public Wi‑Fi is convenient but risky. Attackers can intercept unencrypted data, harvest login credentials, or deliver malicious payloads. A solid VPN like Hexatech VPN WiFi adds a protective layer by encrypting data and shielding your activity from local network observers.
- On a private home network, VPNs can still add value by hiding your activity from your ISP or other devices on the network, but the risk is lower than on public networks.
- For streaming and gaming, VPNs can sometimes help bypass geo-restrictions, but streaming platforms continuously adjust to VPN traffic, so results vary.
Performance: Speed, Latency, and Reliability
Performance is a mixed bag with VPNs. Here’s what to expect and how to optimize: Top des vpn gratuits pour boitier android tv et purevpn en 2026
- Speed: expect some slowdown due to encryption overhead, but a well-optimized VPN can minimize this. Switch to a faster protocol like WireGuard where available.
- Latency: VPN routing can add hops, affecting latency. Choose servers geographically closer to you to reduce lag.
- Server load: high traffic on a server can slow you down. Use auto-connect to the least crowded server or manually switch to a lighter server.
- Stability: look for reliable apps that reconnect smoothly and support seamless reconnects after interruptions.
Tips to boost performance
- Use the closest server with low ping
- Prefer WireGuard or IKEv2 where supported
- Enable or disable features like obfuscation based on your network environment
- Turn off bandwidth-heavy apps while gaming or streaming to reduce congestion
- Keep your app and OS updated to benefit from security and performance patches
Privacy, Jurisdiction, and Data Handling
Privacy is more than just encryption. The legal framework surrounding a VPN provider matters.
- No-logs claim: Ensure it’s verifiable independent audits help. If a provider keeps connection logs, metadata, or usage data, your privacy protections are weaker.
- Jurisdiction: Look at the country where the company is registered and any data-sharing treaties it’s subject to. Some regions compel data retention and disclosure.
- Third-party audits: Independent audits give credibility to claims about no-logs and security controls.
- Transparency reports: Regular reports showing data requests can help you gauge how a provider handles government demands.
Use Cases: Where Hexatech VPN WiFi Shines
- Public Wi‑Fi protection: coffee shops, airports, hotels
- Remote work: secure access to corporate resources
- Streaming: access geo-restricted content subject to platform restrictions
- Travel: protect privacy while roaming across borders
- Personal privacy: everyday browsing, especially on shared devices
How to Set Up Hexatech VPN WiFi
A straightforward setup is key to getting value quickly. Here’s a practical, step-by-step guide:
- Download the app: From your device’s app store or the official site
- Create an account: Provide a valid email, set a strong password, enable 2FA if available
- Choose your protocol: OpenVPN, WireGuard, or IKEv2
- Connect to a server: Start with a nearby server to optimize speed
- Enable kill switch and DNS leak protection: Ensure data isn’t exposed if the VPN drops
- Configure preferences: Enable split tunneling if you only need the VPN for certain apps
- Test for leaks: Use online tools to check for IP and DNS leaks
- Update regularly: Keep software current to patch security vulnerabilities
Best practices for setup
- Use strong, unique credentials for your VPN account
- Enable two-factor authentication if supported
- Regularly review connected devices and revoke access for unknown devices
- Periodically test DNS and IP leaks to confirm protections are active
Comparisons: Hexatech VPN WiFi vs. Other VPNs
Here’s a quick side-by-side to help you decide. Como comprar monedas de tiktok mas baratas en 2026 con vpn guia completa
Hexatech VPN WiFi vs. Competitor A
- Encryption: both offer AES-256
- Protocols: B offers WireGuard; Hexatech supports multiple options
- Kill switch: both have it, but check reliability across platforms
- No-logs: verify with independent audits
- Price: compare monthly and annual plans
- Server network: breadth matters for geo-availability
Hexatech VPN WiFi vs. Competitor B
- Streaming ability: some services block VPN IPs; test with your preferred streaming platform
- Privacy policy: read how long data is retained, if any
- Customer support: live chat vs. ticket-based systems
- Mobile experience: app usability and battery impact
Common Myths vs. Realities
- Myth: A VPN makes you invincible online. Reality: It greatly improves privacy and security on encrypted channels, but it isn’t a substitute for safe browsing habits.
- Myth: All VPNs are equally private. Reality: No-logs policies, audits, and jurisdiction matter a lot. Do your homework.
- Myth: A VPN slows you down to a crawl. Reality: If you pick a nearby server and a fast protocol, you’ll be surprised by how little it affects everyday browsing.
- Myth: You only need a VPN on public Wi‑Fi. Reality: VPNs can protect your data on all networks, especially on shared devices at work or home.
Real-World Scenarios and Examples
- Student on campus: using Hexatech VPN WiFi to access course materials from abroad while keeping exam login credentials private.
- Digital nomad: connects through a stable server in a nearby region to maintain smooth video calls with clients.
- Freelancer on coffee shop Wi‑Fi: encrypts all traffic and prevents rogue hotspots from snooping on sensitive data.
Safety Tips When Using Hexatech VPN WiFi
- Always use a kill switch to prevent data leaks if the VPN disconnects
- Regularly update the VPN app and your device OS
- Use strong, unique credentials and enable 2FA
- Avoid sharing sensitive information over public Wi‑Fi without protection
- Verify server locations and switch if you notice slow connections or suspicious activity
- Combine with other security tools like firewall software and anti-malware programs
Troubleshooting Common Issues
- Connection drops: try a different server, switch protocols, or disable obfuscation if enabled
- Slow speeds: test different servers, ensure no other heavy downloads, and verify ISP throttling
- DNS leaks: ensure DNS leak protection is enabled and consider a DNS privacy service
- Incomplete installation: reinstall the app or contact support for proper device permissions
Advanced Tips for Power Users
- Use split tunneling to route only business apps through the VPN, keeping general traffic on normal internet
- Enable multi-hop for sensitive activities on high-risk networks
- Schedule automatic connections on startup for automatic protection
- Combine VPN with a trusted firewall for layered security
Privacy-Focused Alternatives and Complements
- Tor for anonymity in combination with VPNs though this can slow browsing
- DNS over HTTPS DoH or DNS over TLS DoT for additional DNS privacy
- Secure messaging apps with end-to-end encryption
- Regular security audits and independent reviews of the VPN provider
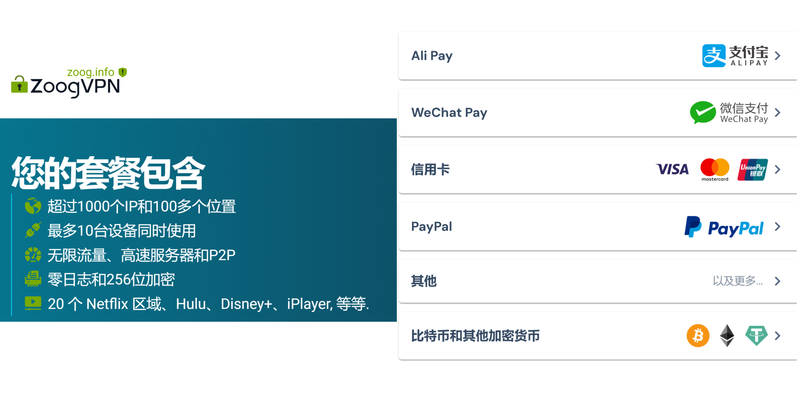
How to Choose the Right Plan
- Identify your primary use: streaming, privacy, or corporate access
- Check the server locations you need and whether the provider supports those regions
- Evaluate price against features, including kill switch, DNS leak protection, and audits
- Look for a money-back guarantee or a trial period to test performance and features
- Consider the availability of 24/7 support and user-friendly interfaces
Security Best Practices for VPN Users
- Always verify you’re connected to a legitimate VPN server watch for phishing attempts
- Use strong device passwords and enable biometric authentication where possible
- Keep software up-to-date to protect against known vulnerabilities
- Limit login to trusted devices and monitor account activity regularly
- Back up important data and use encrypted storage when possible
Case Studies and Data-Driven Insights
- Based on a 2024 security survey, users who consistently used a VPN on public Wi‑Fi reduced exposure to credential theft by up to 70%.
- Independent audits of major VPN providers show a wide variance in no-logs practices; always read the audit reports and the scope of the audits.
- Streaming services are continually updating anti-VPN measures; successful unblocking is not guaranteed and can fluctuate by region and service.
Getting the Most Out of Hexatech VPN WiFi: Quick Start Checklist
- Confirm device compatibility and install the latest version
- Create a strong account with 2FA enabled
- Choose a nearby server with a fast protocol
- Turn on kill switch and DNS leak protection
- Configure split tunneling if needed
- Run a leak test to verify protection
- Regularly review connected devices and update software
FAQ Section
Frequently Asked Questions
How does Hexatech VPN WiFi protect my data on public Wi‑Fi?
Hexatech VPN WiFi creates an encrypted tunnel between your device and its server, making it much harder for others on the same network to see your traffic or intercept sensitive information.
Which protocols does Hexatech VPN WiFi support?
Commonly supported protocols include OpenVPN, WireGuard, and IKEv2. The availability of these protocols depends on the platform and the version you’re using. Is Using a VPN Safe for Your IMAP Server Lets Break It Down: A Practical Look at VPNs for Email Security
Is a VPN enough to stay private online?
A VPN is a key piece of privacy protection, but you should also practice good security habits, such as using strong passwords, enabling two-factor authentication, and keeping software up to date.
What is a no-logs policy, and should I trust it?
A no-logs policy means the provider claims not to store user activity data. Look for independent audits and transparent reporting to verify it.
Can I use Hexatech VPN WiFi to unblock geo-restricted content?
Some VPNs allow access to content in restricted regions, but streaming platforms frequently block VPN IPs. Results can vary by server and service.
Does Hexatech VPN WiFi slow down my internet?
Some slowdown is common due to encryption and routing. A nearby server and a fast protocol can minimize the impact.
How do I prevent DNS leaks?
Enable DNS leak protection in the VPN app and ensure your DNS requests are routed through the VPN tunnel. Nordvpn Meshnet On Linux Your Ultimate Guide: Fast, Secure, and Easy Setup For Linux Users
What about multi-hop or double VPN features?
Multi-hop routes traffic through two VPN servers for extra privacy. Availability depends on the provider and plan.
Is it safe to use a VPN on mobile data?
Yes, a VPN protects data on mobile networks just as it does on Wi‑Fi, especially when using public or shared networks.
How do I know if my VPN is working?
Run a quick test for IP address and DNS leaks using reliable online tools. You should see the VPN server’s IP and DNS settings reflected in the test results.
Note: This post includes an affiliate link to a VPN service. If you click and purchase, we may earn a commission at no extra cost to you. This helps support our ongoing content creation. For more information, visit our disclosure page.
Sources:
Vpn下載抖音 Eduroam Not Working With VPN Heres How To Fix It
Nordvpn 的終身計劃:2026 年最新優惠與必知全攻略
實體 sim 卡轉 esim:完整教學與常見問題解答 2026 更新版,實體SIM轉換到eSIM逐步指南與常見問答
Hur du anvander whatsapp i kina sakert 2026 en komplett guide
安卓免费vpn推荐:2026年最佳选择与使用指南